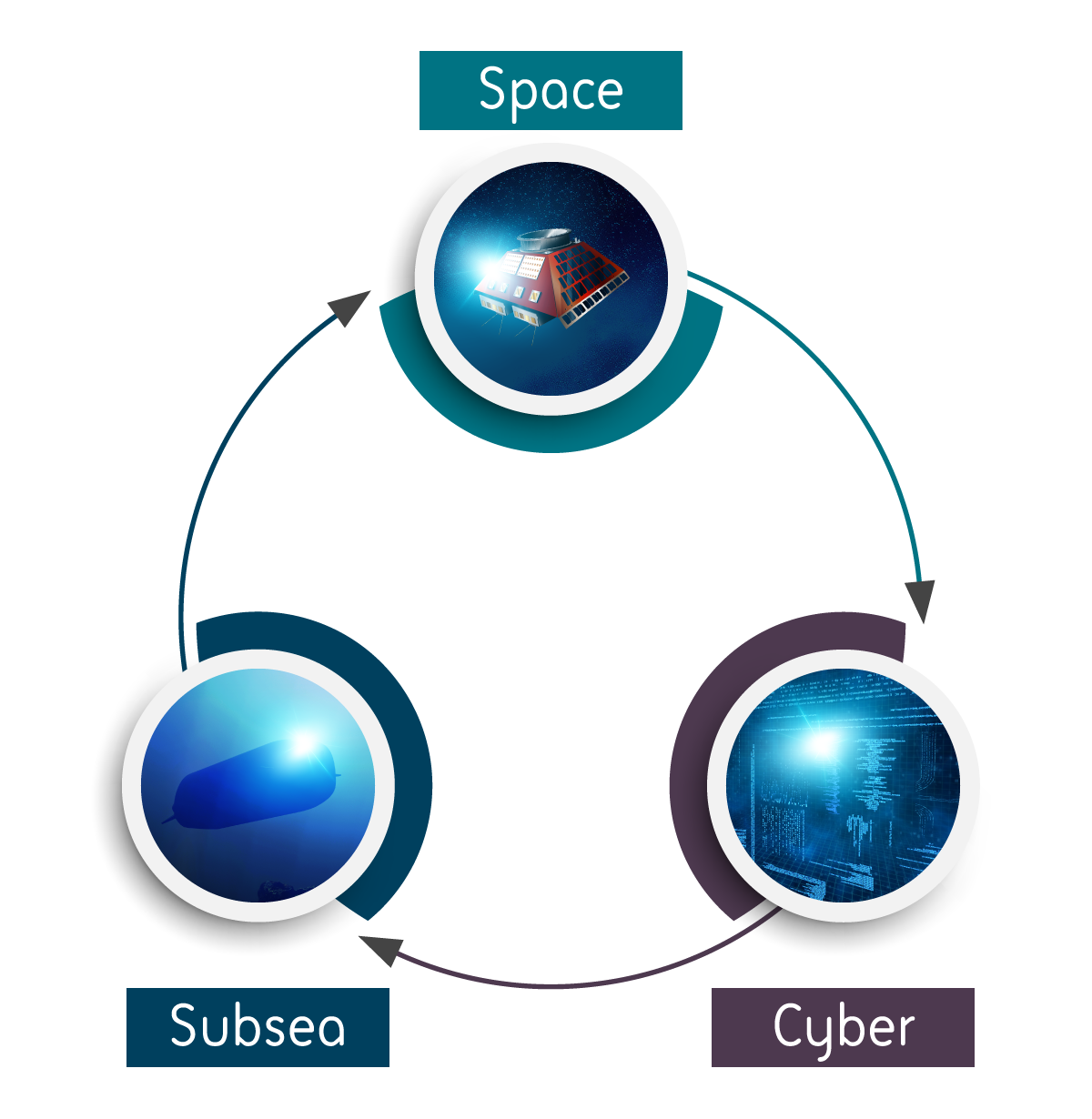
In today’s landscape, a key challenge is how we can work together to collectively secure and realise the benefits of these interconnected domains.
Against a backdrop of technological advances and geopolitical shifts, the traditional defence domains of land, sea and air have been joined by space, cyber and subsea as the modern frontiers of strategic competition.
These domains share common characteristics with the traditional, such as their importance for economic prosperity, the key role they play in critical infrastructure, and their shared use by both civil and military communities.
But they are at the same time distinct, in that they transcend national borders and have unique governance and security challenges. This is increasingly a focus for policy makers, who have responded through various strategy papers and establishing new centres of excellence.
This blog will explore these challenges in more detail, highlighting the interdependencies that exist within this trifecta and the advances required to counter today’s threats.
Shades of grey
The traditional domains of land, sea and air very much operate in the physical world. Any defensive or offensive activities are generally visible and attributable.
This is not the case for space, cyber and subsea. These new-age domains all lend themselves to subthreshold warfare. Hostile actors can operate in ‘the grey zone’ of conflict, characterised by the UK Ministry of Defence as "a murky area, consisting of everything which isn’t full on conflict, but isn’t exactly an innocent act either." Typical examples of grey zone activity include espionage, sabotage, and misinformation campaigns.
Events and incidents in the grey zone can be hard to detect, hard to contextualise, and may be impossible to attribute. Space, cyber and subsea are opaque domains, meaning hostile actors can hide their activities and disrupt their adversaries in more subtle ways.
Indeed, the subsea domain could be considered the ultimate place to hide given the inherent visibility and access challenges that accompany underwater operations, while the sheer scale of space and cyber provides substantial camouflage for those able and willing to exploit it.
Adding to the ambiguity is the fact that these domains are beyond national jurisdictions and boundaries. They are a ‘global commons’, subject to international treaties and cooperation but essentially beyond any nation’s control – further enforcing their suitability for subthreshold warfare. It’s therefore no surprise that malign state and non-state threat actors are increasingly active across all three.
A symbiotic relationship
Another key characteristic of the space, cyber, subsea trifecta is how dependent they are on each other.
For example, in the subsea domain there is a growing threat to critical underwater infrastructure (CUI), such as the fibre optic cables which are the backbone of the internet. The cyber domain therefore is highly dependent on the security of the seabed and wider underwater environment.
Maintaining security of the subsea domain relies on space-based assets which can detect maritime anomalies in wide areas of ocean, monitoring activities on the surface of the sea to identify potential underwater threats. However, these satellites and their ground infrastructure are in turn dependent on strong cyber security, which has been subject to attack in recent years as hostile states look to disrupt space operations and capabilities.
A prominent example is Russia’s targeted attack of American satellite company Viasat in the hours before the full-scale invasion of Ukraine (as outlined here in the MIT Technology Review). This resulted in a significant loss of communication in the earliest days of the war for the Ukrainian military, and clearly demonstrated how space-based capabilities can be undermined through targeted cyber-attacks.
The interdependency between these domains is a level of complexity which cannot be appreciated by examining a single domain in isolation. Approaches to securing the system as a whole need to be developed, along with the enabling technologies and public-private partnerships.
Countering threats
Given this context and the threats facing these new-age domains, what mechanisms can be implemented to improve their security and build on learnings from other domains?
Attribution is a key capability, as without this there can be no deterrence. This is a well-established challenge in the cyber domain – whether we’re talking about it from a technical (i.e. forensic evidence) or political (i.e. publicly naming culprits) perspective. Often, attribution in cyber is a joint endeavour, with the technical elements coming from private sector firms, and the measures (indictments, sanctions, disruptions) coming from government agencies.
The cyber domain has an advantage in that systems have been setup for logging activity. The evidence of any cyber-attack exists somewhere; the challenge is finding it. With this in mind, the question becomes how can we apply this process to the space and underwater domains which don’t intrinsically have technical logs?
In subsea, no-one can monitor activities without the right infrastructure in place, highlighting a need to implement the capability for technical attribution. Such ‘maritime domain awareness’ can be partly enabled by space, providing a vantage point to monitor surface-level activities and infer what could be happening underwater. But we also need greater investment in underwater monitoring capabilities – networks of sensors which can provide subsea intelligence.
Along with real-time monitoring via space, we also need real-time monitoring of space itself. Space domain awareness is advancing as a field, both in the public and private sectors. Better data and new technologies which enable both on-board and off-board analytics will help raise situational awareness and improve security.
Of course, ensuring resilience in any one of these domains is no mean feat, let alone all three. As this new age of competition continues to evolve, success will depend on how public and private sectors can work together to collectively secure, and thereby realise the benefits these interconnected domains have to society.
